Manufacturing companies face unprecedented cybersecurity threats in 2026. Recent industry data reveals alarming success rates for cyberattacks targeting production facilities, with most breaches occurring due to preventable vulnerabilities that traditional IT management approaches consistently miss.
The root cause extends beyond basic security gaps. Manufacturing environments present unique challenges that require specialized expertise: expertise that most internal teams lack and cannot develop quickly enough to counter evolving threats.
The Manufacturing Cybersecurity Crisis
Manufacturing ranks as the third most targeted industry for cyberattacks. Attack vectors have expanded dramatically as smart factory initiatives connect operational technology (OT) systems to corporate networks without adequate security frameworks.
Consider these concerning trends:
- 258 ransomware incidents targeted critical manufacturers in 2024 alone
- 95% of security breaches result from human error in manufacturing environments
- 18% of penetration testing findings in manufacturing reveal serious vulnerabilities
- Median resolution time for security issues reaches 122 days: the worst performance across all industries

Legacy systems compound these challenges. Most manufacturing equipment was designed decades ago without security considerations. These systems cannot receive security patches without risking operational disruption, creating permanent vulnerability windows that attackers actively exploit.
Why Traditional IT Management Fails Manufacturing
Manufacturing cybersecurity requires specialized knowledge that combines industrial operations expertise with advanced security frameworks. Internal IT teams typically focus on corporate systems while lacking deep understanding of production environment risks.
Standard cybersecurity approaches fail because they treat manufacturing like any other business vertical. This fundamental misunderstanding creates gaps in:
Operational Technology Integration: Corporate security tools often cannot monitor or protect industrial control systems without disrupting production workflows.
Risk Assessment: Traditional frameworks underestimate the operational impact of security incidents on continuous production environments.
Compliance Requirements: Manufacturing faces industry-specific regulations that require specialized compliance expertise.
Vendor Management: Production environments involve complex vendor ecosystems with varying security maturity levels.
Most manufacturers attempt to address these challenges by expanding internal capabilities. This approach consistently fails because building specialized expertise requires years of focused development while threats evolve rapidly.
The Fractional CIO Manufacturing Advantage
Fractional CIO manufacturing solutions provide immediate access to executive-level expertise specifically designed for production environments. Unlike traditional consulting approaches, fractional CIOs integrate directly into your leadership team while bringing proven frameworks developed across multiple manufacturing environments.
This model delivers three critical advantages:
Immediate Expertise: Access specialized knowledge without the time investment required to develop internal capabilities.
Cost Efficiency: Obtain executive-level strategic oversight at a fraction of full-time executive costs.
Proven Frameworks: Implement security approaches that have been tested and refined across diverse manufacturing environments.

Fractional CIOs understand the unique balance between security requirements and operational continuity that manufacturing demands. They bring experience managing IT-OT integration challenges while maintaining production uptime.
The Manufacturing IT Security Review Framework
Effective manufacturing cybersecurity requires a systematic approach that addresses both corporate and operational technology environments. The following framework provides the foundation for comprehensive security assessment and implementation.
Phase 1: Asset Discovery and Risk Assessment
Begin with complete visibility into your technology landscape. Manufacturing environments typically contain:
- Corporate IT systems (ERP, email, file servers)
- Industrial control systems (SCADA, DCS, PLC)
- Connected devices (sensors, cameras, IoT equipment)
- Network infrastructure (switches, routers, wireless access points)
Document each asset's function, network connections, and current security controls. Identify systems that cannot be patched or upgraded without operational impact.
Assess risk levels by evaluating potential operational impact alongside standard cybersecurity metrics. A vulnerability in a critical production system requires different prioritization than similar vulnerabilities in corporate systems.
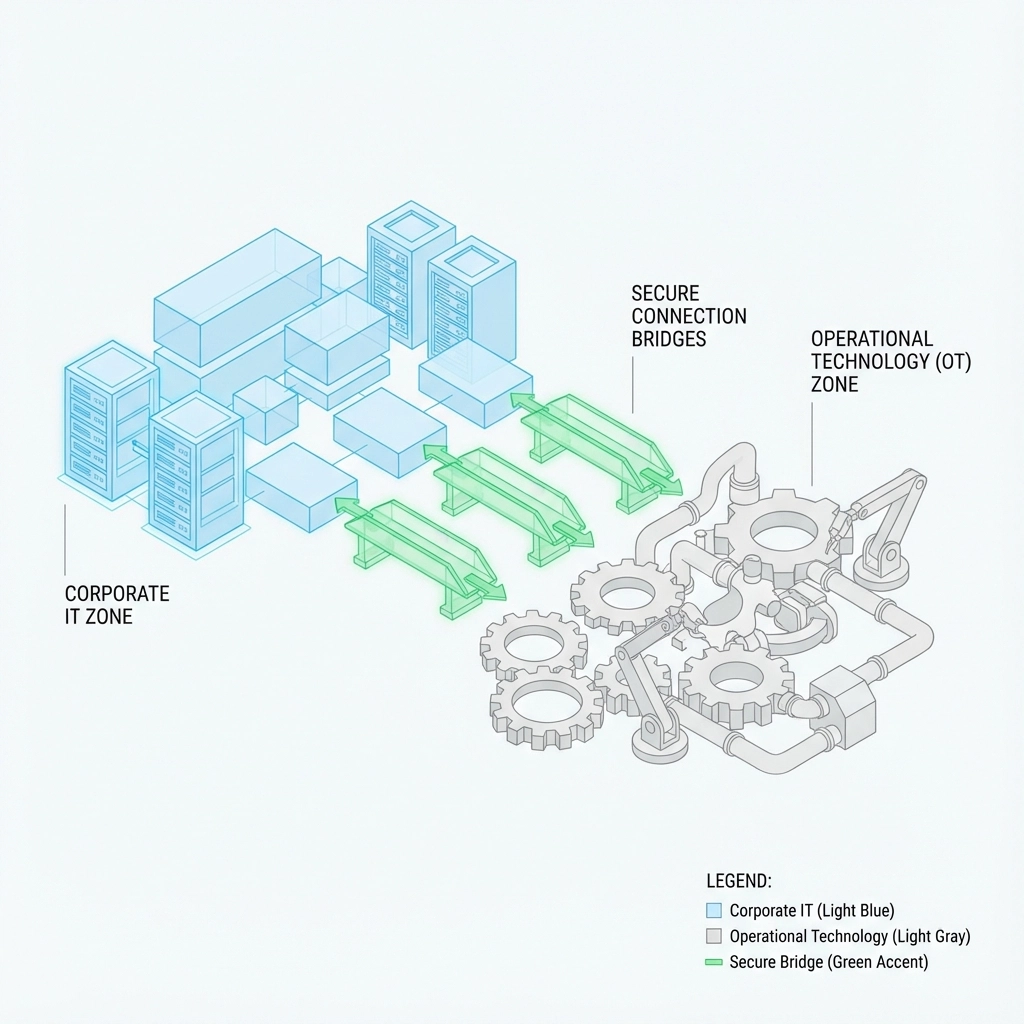
Phase 2: IT-OT Integration Security
Examine connections between corporate and operational networks. Most security breaches in manufacturing begin in corporate systems before moving laterally into production environments.
Implement network segmentation that maintains operational connectivity while preventing unauthorized access. This requires specialized knowledge of industrial protocols and communication requirements.
Review remote access capabilities for vendors and support personnel. Manufacturing often requires external access for maintenance and troubleshooting, creating additional attack vectors that need careful management.
Phase 3: Vendor and Supply Chain Security
Manufacturing operations depend on complex vendor ecosystems. Each vendor relationship creates potential security exposure that requires active management.
Evaluate vendor security practices through formal assessment processes. Require security certifications and regular compliance reporting from critical vendors.
Implement secure communication channels for vendor interactions. Standard email and file sharing approaches often lack sufficient protection for sensitive operational information.
Establish incident response procedures that include vendor coordination. Security incidents may require immediate vendor support, particularly for specialized industrial systems.
Phase 4: Employee Training and Access Control
Manufacturing environments combine office workers, production staff, and external contractors with varying technology experience levels. Standard cybersecurity training approaches often fail because they do not address manufacturing-specific scenarios.
Develop role-specific training programs that address actual work environments. Production staff face different security challenges than office workers and require targeted guidance.
Implement access controls that support operational workflows while maintaining security boundaries. Overly restrictive controls can force staff to develop workarounds that create new vulnerabilities.
Review access requirements regularly as roles and responsibilities evolve. Manufacturing often involves shift work and temporary staffing that complicates traditional access management approaches.
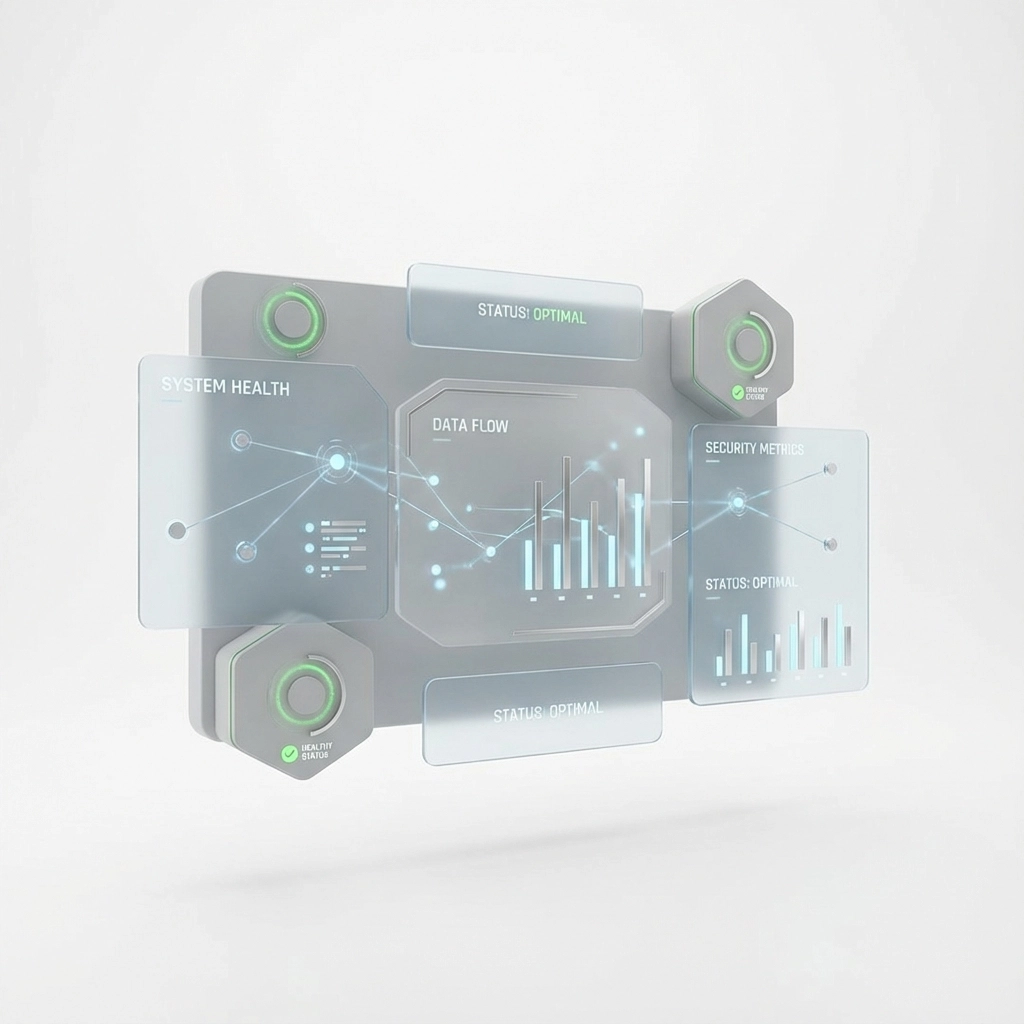
Implementing Continuous Security Monitoring
Manufacturing requires security monitoring approaches that accommodate operational requirements. Traditional security tools may generate alerts that disrupt production or require response capabilities that conflict with operational priorities.
Deploy monitoring solutions specifically designed for industrial environments. These tools understand normal operational patterns and can distinguish between legitimate industrial activity and potential security threats.
Establish response procedures that prioritize operational continuity while addressing security concerns. Security incidents in manufacturing often require coordination between IT, operations, and safety teams.

Create communication protocols that ensure rapid information sharing without disrupting production workflows. Security teams need operational context to make informed decisions during incident response.
Measuring Security Program Effectiveness
Manufacturing cybersecurity programs require metrics that reflect operational realities alongside traditional security measurements.
Track mean time to detection and response for security incidents, with separate measurements for corporate and operational systems. Industrial systems may require different response approaches that affect timing metrics.
Monitor training effectiveness through simulated scenarios that reflect actual manufacturing environments. Office-based simulations may not accurately assess security preparedness in production settings.
Evaluate vendor compliance through regular assessments and audit results. Vendor security posture directly affects your overall security position and requires ongoing attention.
Measure operational impact of security controls through production metrics. Security implementations that negatively affect production efficiency require adjustment or replacement.
Building Long-Term Manufacturing Digital Transformation
Manufacturing digital transformation initiatives often introduce new security challenges while creating opportunities for improved security posture. Fractional CIO leadership ensures that transformation projects incorporate security considerations from the planning phase rather than adding security as an afterthought.
Modern manufacturing increasingly depends on data-driven decision making that requires secure data collection and analysis capabilities. Security frameworks must evolve to protect these new capabilities while enabling the operational insights that drive competitive advantage.
Cloud adoption in manufacturing requires specialized approaches that address regulatory requirements and operational continuity needs. Standard cloud security approaches may not adequately address manufacturing-specific requirements.
Next Steps for Manufacturing Leaders
Manufacturing cybersecurity requires immediate action combined with long-term strategic planning. Begin with comprehensive security assessment that addresses both corporate and operational environments.
Evaluate your current IT leadership capabilities against the specialized requirements that manufacturing cybersecurity demands. Consider fractional CIO services if internal capabilities cannot address these unique requirements quickly enough to counter evolving threats.
Implement security monitoring and response capabilities designed specifically for manufacturing environments. Standard corporate security tools often cannot provide adequate protection for industrial systems.
Develop vendor management processes that address security requirements without disrupting critical operational relationships. Manufacturing success depends on effective vendor partnerships that must include appropriate security frameworks.
For manufacturing leaders ready to implement comprehensive cybersecurity frameworks, Bailey & Associates provides fractional CIO services specifically designed for production environments. Our proven approaches balance security requirements with operational continuity to protect your manufacturing operations while enabling continued growth and digital transformation initiatives.
Related Service: Fractional CIO/IT Director — Learn how Bailey Associates can help your manufacturing business.
