When ransomware hits a manufacturing facility, every minute of downtime costs thousands in lost production, missed deliveries, and potential safety risks. Unlike office environments where employees can work from laptops, manufacturing operations grind to a complete halt when critical systems go down. This reality makes manufacturing IT strategy fundamentally different from standard business recovery planning.
A fractional CIO manufacturing specialist understands these unique pressures and can guide your recovery with the speed and precision that factory operations demand. Here's your step-by-step survival guide when the worst happens.
The Critical First 4 Hours: Immediate Response Protocol
The moment you detect ransomware, your response determines whether you'll be down for days or weeks. Manufacturing environments have interconnected systems where infection can spread rapidly from office networks to production control systems.
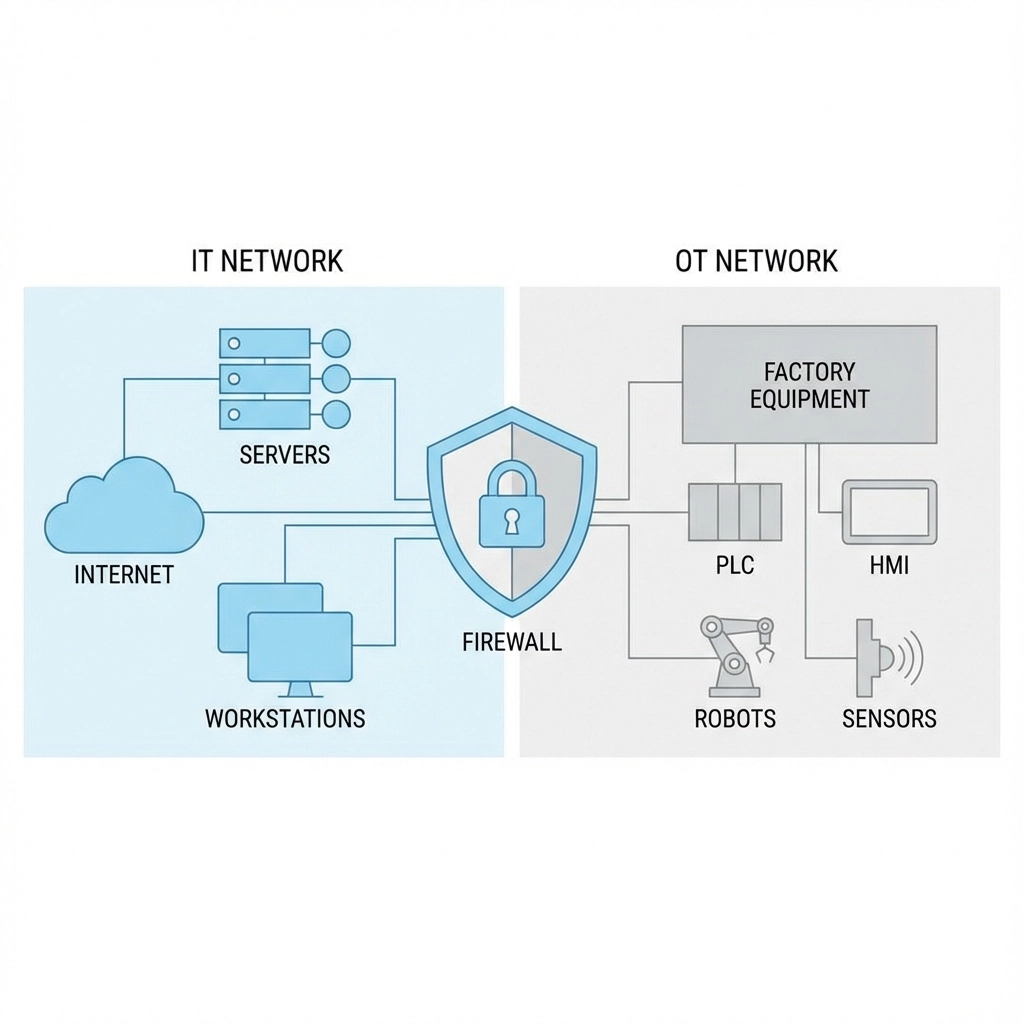
Isolate infected systems immediately. Physical disconnection is non-negotiable: pull ethernet cables and disable WiFi on any compromised machines. This prevents lateral movement to your manufacturing execution systems (MES), programmable logic controllers (PLCs), or SCADA networks that control your production lines.
Keep infected machines powered on despite the temptation to shut them down. You'll need these systems for forensic investigation to understand how the attack occurred and prevent reinfection through the same vulnerability.
Disconnect backup systems before they become compromised. Many ransomware variants specifically target backup infrastructure to force victims into paying ransoms. Immediately isolate your backup servers and halt any scheduled backup jobs that could overwrite clean data with encrypted files.

Document everything from the start. Note which systems showed symptoms first, unusual network activity, and any error messages. This documentation becomes crucial for both recovery planning and potential insurance claims.
Activate your incident response team immediately. In manufacturing, this includes not just IT personnel but production managers, quality control, safety officers, and supply chain coordinators. Everyone needs to understand the scope and expected timeline for recovery.
Strategic Decision Making: Pay or Rebuild?
Between 24-72 hours after the attack, you'll face the critical decision that can make or break your recovery timeline. This is where fractional CIO manufacturing expertise proves invaluable: someone who understands both cybersecurity principles and manufacturing operational requirements.
Assess your backup integrity first. Quality backups make the decision simple: rebuild rather than pay. However, many manufacturers discover their backups are incomplete, corrupted, or include infected files that will reintroduce the malware.
A fractional CIO will evaluate your backup strategy across three critical dimensions:
- Recency: How much production data will you lose?
- Completeness: Are your MES configurations, PLC programs, and HMI interfaces backed up?
- Integrity: Can you verify backups are clean and bootable?
Consider your production schedule impact. Unlike office workers who can remain productive with temporary workarounds, manufacturing has fixed delivery commitments, just-in-time inventory requirements, and potential safety implications from rushed restarts.
Calculate the true cost of downtime including lost production, expedited shipping, penalty clauses, and potential customer relationship damage. Compare this against ransom demands, but remember that paying provides no guarantee of full data recovery or protection from future attacks.

Safe Recovery and Restoration
When rebuilding from backups, manufacturing environments require specialized recovery procedures that protect both data integrity and operational safety.
Create a clean room environment completely isolated from your production network. This quarantined space allows you to restore and test systems without risking reinfection of your entire facility.
Prioritize critical manufacturing systems first. Not all systems are equally important for production restart. Focus initial recovery efforts on:
- Safety systems and emergency shutdowns
- Core production line controls
- Quality management systems
- Inventory and shipping systems
Test restored systems thoroughly before production restart. This includes verifying PLC programs, HMI functionality, and communication between manufacturing systems. A premature restart with partially recovered systems can cause expensive equipment damage or product quality issues.
Reset all credentials and access controls. This means every password, service account, and access token across both IT and operational technology (OT) systems. Many manufacturers overlook SCADA passwords, PLC access codes, and service accounts that connect manufacturing systems to enterprise networks.
Post-Recovery Hardening: Preventing the Next Attack
Recovery is only half the battle. Without proper hardening, you're vulnerable to reinfection through the same attack vector or new vulnerabilities.
Segment your IT and OT networks immediately. Most manufacturing ransomware attacks start in office networks and spread to production systems through poor network segmentation. Implement proper firewalls and network access controls between enterprise and manufacturing systems.
Deploy immutable backup infrastructure. Traditional backup systems that maintain network connectivity can be compromised during ransomware attacks. Implement air-gapped backups, write-once-read-many (WORM) storage, or cloud-based solutions with immutable snapshots.

Patch everything before bringing systems online. This includes not just servers and workstations, but also industrial control systems, HMIs, and any IoT devices on your factory floor. Many manufacturers run outdated systems because they fear production disruption, creating easy targets for attackers.
Enable multi-factor authentication everywhere. This includes remote access systems, administrative accounts, and any cloud-based manufacturing applications. Remote access to manufacturing systems has become a primary attack vector, especially with increased adoption of remote monitoring and maintenance.
Why Manufacturing Needs Specialized Fractional CIO Guidance
Manufacturing ransomware recovery differs significantly from standard business continuity planning. A fractional CIO with manufacturing experience brings several critical advantages during crisis situations.
Understanding of operational technology. Manufacturing systems include PLCs, SCADA networks, and industrial protocols that require specialized knowledge for safe recovery. A fractional CIO familiar with these systems can guide recovery without creating safety risks or equipment damage.
Regulatory compliance awareness. Manufacturing operations often must maintain compliance with FDA, ISO, or industry-specific regulations. Recovery procedures must preserve audit trails and maintain compliance documentation to avoid regulatory violations during restart.
Supply chain coordination. Manufacturing disruptions ripple through complex supply chains affecting customers, suppliers, and logistics partners. An experienced fractional CIO can coordinate communication and contingency planning with external stakeholders.
Building Long-term Resilience
Surviving one ransomware attack successfully doesn't guarantee immunity from future incidents. Manufacturing operations need ongoing manufacturing IT strategy focused on operational resilience.
Regular backup testing and validation. Schedule quarterly recovery tests that include full system restoration and production line restart procedures. Many manufacturers discover backup failures only during actual emergencies.
Continuous security monitoring. Implement monitoring solutions that cover both IT and OT networks. Manufacturing environments often have unique network traffic patterns that require specialized monitoring approaches.
Incident response plan refinement. Regular tabletop exercises help manufacturing teams practice coordination between IT, operations, safety, and management during crisis scenarios.
Vendor risk management. Manufacturing operations depend heavily on third-party systems for ERP, MES, and specialized manufacturing applications. Ensure vendors maintain appropriate security standards and can support emergency recovery procedures.
The reality of manufacturing ransomware attacks is that traditional IT recovery approaches often fail in industrial environments. Production systems, safety requirements, and operational complexity demand specialized expertise that most internal IT teams lack.
A fractional CIO with manufacturing experience provides the strategic guidance needed to survive ransomware attacks while maintaining operational safety and minimizing production disruption. The investment in specialized expertise proves worthwhile when measured against the true cost of extended production downtime and potential safety incidents.
Recovery from ransomware isn't just about restoring data: it's about safely restarting complex manufacturing operations while building long-term resilience against future attacks. With proper planning, specialized expertise, and proven recovery procedures, manufacturers can survive ransomware attacks and emerge with stronger, more secure operations.
Related Service: Fractional CIO/IT Director — Learn how Bailey Associates can help your manufacturing business.
